Scalable and Secure Systems
 I guess the current AI (machine learning) madness made me think about "the next big thing" in IT - which according to Google, IBM and others might just be Quantum Computing. It turned out to be a steep learning curve and I decided to start with some basics in quantum theory before diving into the Quiskit framework for example. Here is what I learned from Sean Carrols book onqQuantum Theory.
I guess the current AI (machine learning) madness made me think about "the next big thing" in IT - which according to Google, IBM and others might just be Quantum Computing. It turned out to be a steep learning curve and I decided to start with some basics in quantum theory before diving into the Quiskit framework for example. Here is what I learned from Sean Carrols book onqQuantum Theory.
I have added the option to set the configuration values (mac and key) for the devices via a SD-card which contains three files.
Can we support the healing process of stroke victims with computer game equipment? And would a AI-glasses allow a better documentation of surgery in dental clinics? Two ideas that might fly in university project or thesis work - not least to the reduced price tag of consumer electronics compared to medical equipment.
 This final part describes how the software for the esp32c3 with the round display can be patched for your own devices. You will need to find the mac addresses of your devices either through the battery app or through Nordic mobile connect app and replace the dummy values in the software.
This final part describes how the software for the esp32c3 with the round display can be patched for your own devices. You will need to find the mac addresses of your devices either through the battery app or through Nordic mobile connect app and replace the dummy values in the software.
And for the Victron MPPT and Booster the respective keys need to be found in the Victron app and patched. And a warning about BMS values is given to avoid surprises especially when the camper is in winter storage.
This part describes a small workaround for the unbonded battery problem. An  esp32c3 together with a round display from Seed Studio is used to create a permanent connection with the battery. Hardware and software are explained. It took a while to understand BLE better and of course: c++ nowadays is just as ugly as it was in the nineties. It took me a while to get used to it again after so many years with garbage collected languages. The round display (even with touch) turned out to be an ideal companion to the little Arduino. Finally I got carried away a bit and implemented a clock, a menu, a debug screen and some other stuff. The whole thing is not finished yet because I am still experimenting with extended BLE advertisements and I would like the device to enter deep sleep .
esp32c3 together with a round display from Seed Studio is used to create a permanent connection with the battery. Hardware and software are explained. It took a while to understand BLE better and of course: c++ nowadays is just as ugly as it was in the nineties. It took me a while to get used to it again after so many years with garbage collected languages. The round display (even with touch) turned out to be an ideal companion to the little Arduino. Finally I got carried away a bit and implemented a clock, a menu, a debug screen and some other stuff. The whole thing is not finished yet because I am still experimenting with extended BLE advertisements and I would like the device to enter deep sleep .
La Sicilia e la Cosa Nostra - non cè l'una senza l'altra. Ho trovato un bel libro in una bellissima libreria a Palermo.  Il foto: Il monumento per le vittime della mafia al porto di Palermo - e ne sono stati moltissimi: giudici, poliziotti e altri. Mi raccomando anche visitare Corleone con il museo pubblico e la "casa della mafia".
Il foto: Il monumento per le vittime della mafia al porto di Palermo - e ne sono stati moltissimi: giudici, poliziotti e altri. Mi raccomando anche visitare Corleone con il museo pubblico e la "casa della mafia".
.
.
I got a rude awakening when I realized, that my wonderful new LifePo4 battery does not have any protection for its BMS. This is the first part of two postings about this problem. The first part gives an overview of the problem, a short discussion of its risks and who might be in danger. It ends with a surprise for those batteries that seem to be safe because they are protected by a password. There are apps which simply remove the password protection. This makes you wonder a lot about the security of those batteries in general. I guess it would be time for a camper pen-test. Not to forget we are talking about devices which can deliver several hundreds of amperes!
does not have any protection for its BMS. This is the first part of two postings about this problem. The first part gives an overview of the problem, a short discussion of its risks and who might be in danger. It ends with a surprise for those batteries that seem to be safe because they are protected by a password. There are apps which simply remove the password protection. This makes you wonder a lot about the security of those batteries in general. I guess it would be time for a camper pen-test. Not to forget we are talking about devices which can deliver several hundreds of amperes!
Currently many vintage campers are converted to LifePo4 batteries. I have done the same and this little article collects some of the experiences made during that process. It took me roughly 3 weeks to install a large battery, new MPPT charger, booster and land line charger together with two new compressor based fridges. It was not cheap but we have not used the 230V cable since (:-). Those batteries change everything and - my prediction - will lead to gas-free fully autonomous campers based on 24V or 48V installations. 12V is simply getting killed by the huge amperes now available in batteries.
 I won't talk too much here about this little gem of a book as I have written the foreword for it. Except that it is pleasingly short and to the point. And that it is fun to read because it is full of stories due to a live spent in software development. The author, Dr. Bernhard Scheffold provides a clear understanding of the process and culture behind Devops and by doing so clarifies a lot of misconceptions about it. You won't get lost in technicalities but you will gain the knowledge to implement DevOps even in complicated, multi-partner contexts. If you hear statements like "we don't do deployments on Friday" in your organization: this book is for you and your boss! If your colleagues frequently shortcut your deployment pipeline only to end up with rollbacks and frustrated customers: this book is for you and your boss!
I won't talk too much here about this little gem of a book as I have written the foreword for it. Except that it is pleasingly short and to the point. And that it is fun to read because it is full of stories due to a live spent in software development. The author, Dr. Bernhard Scheffold provides a clear understanding of the process and culture behind Devops and by doing so clarifies a lot of misconceptions about it. You won't get lost in technicalities but you will gain the knowledge to implement DevOps even in complicated, multi-partner contexts. If you hear statements like "we don't do deployments on Friday" in your organization: this book is for you and your boss! If your colleagues frequently shortcut your deployment pipeline only to end up with rollbacks and frustrated customers: this book is for you and your boss!
If you are studying software development: I have used examples from early drafts of this book in my lectures successfully. The book uses examples and stories to transport the experience from many years of software development.
There is also a BLOG and a linked in page for discussions.
Well, the time has come to say goodbye at HdM. I will never forget the way my colleagues and my students and my alumnis at HdM made the last summer term unforgettable!! Thanks for all the good wishes and praise I have received in those last weeks. I surely had the best possible job ever and the best environment one could imagine. Now I am trying to find my way into retirement somehow and maybe this site gets some new content in a while.
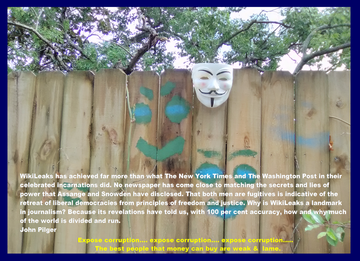 Perhaps you would like to join one of the many petitions to free Julian Assange ? He and Snowden have uncovered more political and war crimes than all the newspapers together. (image copyright: Om777om / CC BY-SA (https://creativecommons.org/licenses/by-sa/4.0)). Some links to leaks on war crimes etc. can be found here .
Perhaps you would like to join one of the many petitions to free Julian Assange ? He and Snowden have uncovered more political and war crimes than all the newspapers together. (image copyright: Om777om / CC BY-SA (https://creativecommons.org/licenses/by-sa/4.0)). Some links to leaks on war crimes etc. can be found here .
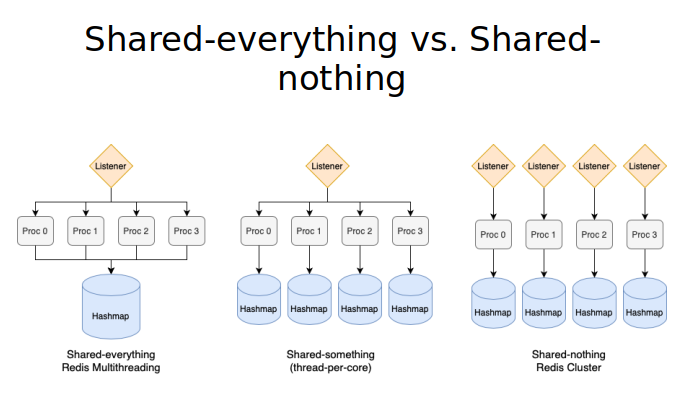 Multi-core has brought us many challenges: The high cost of locking is destroying our performance or throughput. And when we go down the partitioning road and try to avoid sharing things we discover that a high variance in request load or execution time destroys our tail latency. So what works best for Redis and many other network driven applications? ARE THEY really network driven or could they even be compute bound? The answers to those questions can be found in the thesis of Lucas Crämer How can Highly Concurrent Network-Bound Applications benefit from modern multi-core CPUs?. He did not only look at code in Redis, Tokio and other applications but measured response times and throughput with a specially developed measurement harness. And he comes to some clear results with respect to sharing or not. And while doing so explains a lot of other interesting things that he came across in his research: SPSC queues, IO-uring, thread-per core and how to use queuing theory concepts successfully. Take a look to understand I/O and process models on multi-core.
Multi-core has brought us many challenges: The high cost of locking is destroying our performance or throughput. And when we go down the partitioning road and try to avoid sharing things we discover that a high variance in request load or execution time destroys our tail latency. So what works best for Redis and many other network driven applications? ARE THEY really network driven or could they even be compute bound? The answers to those questions can be found in the thesis of Lucas Crämer How can Highly Concurrent Network-Bound Applications benefit from modern multi-core CPUs?. He did not only look at code in Redis, Tokio and other applications but measured response times and throughput with a specially developed measurement harness. And he comes to some clear results with respect to sharing or not. And while doing so explains a lot of other interesting things that he came across in his research: SPSC queues, IO-uring, thread-per core and how to use queuing theory concepts successfully. Take a look to understand I/O and process models on multi-core.
The tracks for NoCode/LowCode and WebAssembly are now online. It was a very interesting Friday afternoon and showed clearly the high potential behind both approaches. When you have access to the proper data predection becomes rather easy in many cases: I know about several other projects targeting NoCode/LowCode right now and I think model driven development will play (again) a much bigger role in the future. Or as two of my Master students told me: "We do way too much copy/paste in frontend and backend. They are trying to generate both e.g. to access Firebase. Webassembly as the global execution platform has become a reality. Take a look at webnetes.dev to see it used for doing distributed machine learning and much more. And don't miss the ever growing popularity of IPFS!
A not so optimistic piece on critical developments both outside and inside the University.
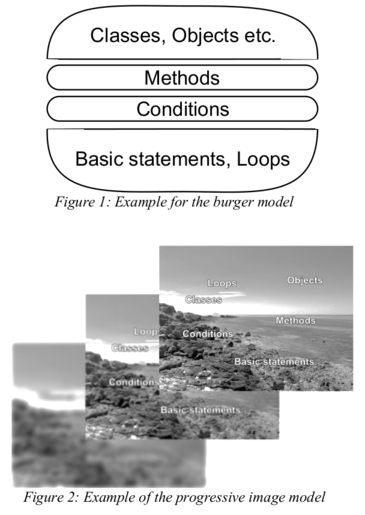 How do you see software development in the 21st century? Here is how we (Dr. Tobias Jordine and myself) designed and ran an advanced software course at HdM. Feedback very much appreciated.
How do you see software development in the 21st century? Here is how we (Dr. Tobias Jordine and myself) designed and ran an advanced software course at HdM. Feedback very much appreciated.
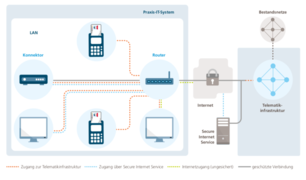 Is the german health infrastructure that is currently rolled out in many practices really up to date or a disaster waiting to happen? If your are interested in a thesis on this politically and technically challenging topic, let me know. The current solutions are either extremely unsafe or - if hardened - not workable. A security analysis and alternative architectures (cloud?) are required.
Is the german health infrastructure that is currently rolled out in many practices really up to date or a disaster waiting to happen? If your are interested in a thesis on this politically and technically challenging topic, let me know. The current solutions are either extremely unsafe or - if hardened - not workable. A security analysis and alternative architectures (cloud?) are required.
A short piece on the concept of disruption against the dark background of Yuval Harari's 21 Lessons for the 21st century.
A few open questions that had been bothering me for quite a while - and an unexpected re-discovery of the past.
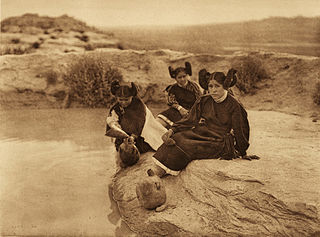 (Hopi image: Edward S. Curtis [Public domain], via Wikimedia Commons) I remember reading Benjamin Lee Whorf's famous book on language, thinking and perception of reality and being quite impressed about his discoveries in the Hopi language and culture. Later his methods were seriously questioned and rejected. But in my mind his theory on how the structure of our language influences our thinking prevailed. Now, Lera Boroditsky wrote How Does Our Language Shape The Way We Think. And it looks like things have changed a bit...
(Hopi image: Edward S. Curtis [Public domain], via Wikimedia Commons) I remember reading Benjamin Lee Whorf's famous book on language, thinking and perception of reality and being quite impressed about his discoveries in the Hopi language and culture. Later his methods were seriously questioned and rejected. But in my mind his theory on how the structure of our language influences our thinking prevailed. Now, Lera Boroditsky wrote How Does Our Language Shape The Way We Think. And it looks like things have changed a bit...
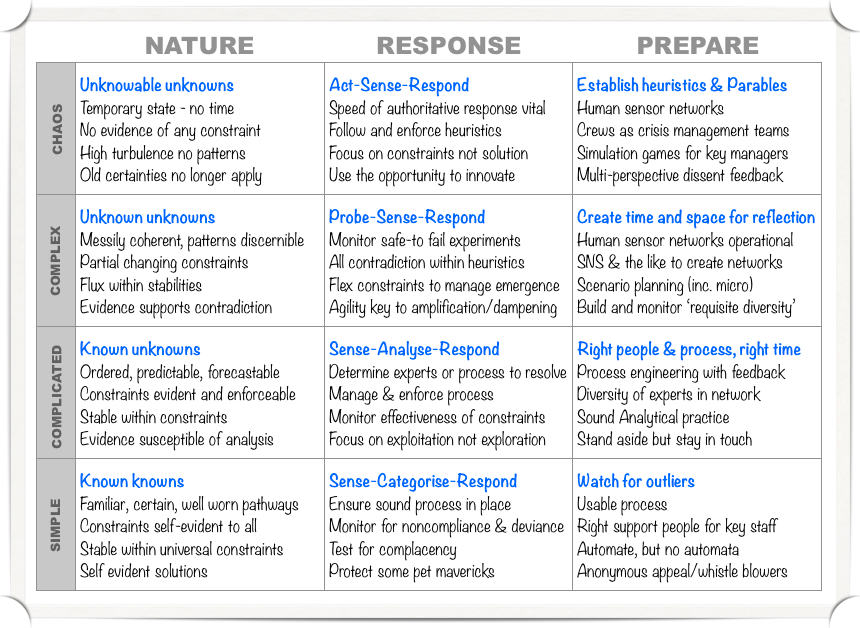 (table from Brougham's paper). As part of our master journal club we read a little piece by Greg Brougham on Cynefin, the famous framework covering the ordered and unordered world. And while Cynefin is interesting in itself, I was reading the "Book of Why" by Judea Pearl at the same time and noticed something: The do-calculus by Pearl is geared toward understand causal relations between things. It is based on intervention. The Cynefin framework goes from "sensing" in the ordered domain towards "probe or act, sense, respond" in the complex and chaotic domain. Well, I guess detecting causality IS deeply connected with doing or acting in every case that is not already well-known. More on the do -calculus in a later article.
(table from Brougham's paper). As part of our master journal club we read a little piece by Greg Brougham on Cynefin, the famous framework covering the ordered and unordered world. And while Cynefin is interesting in itself, I was reading the "Book of Why" by Judea Pearl at the same time and noticed something: The do-calculus by Pearl is geared toward understand causal relations between things. It is based on intervention. The Cynefin framework goes from "sensing" in the ordered domain towards "probe or act, sense, respond" in the complex and chaotic domain. Well, I guess detecting causality IS deeply connected with doing or acting in every case that is not already well-known. More on the do -calculus in a later article.
On a sideline: I watched a talk by John Snowden, one of the inventors of Cynefin, at the Domain-Driven-Conference Amsterdam 2018 and he made a little remark that shocked me: When he talked about evolutionary mechanisms in the context of complexity, he mentioned a talk he gave to US upper managment in Texas. And he was asked to NOT MENTION EVOLUTION, as it might hurt attendants. More than 50% of US citiziens seem to deny evolution as a principle of nature. Many years ago I thought that we had left religion as a major problem of the future behind us. I was wrong. Humanity is far from accepting scientific thinking.
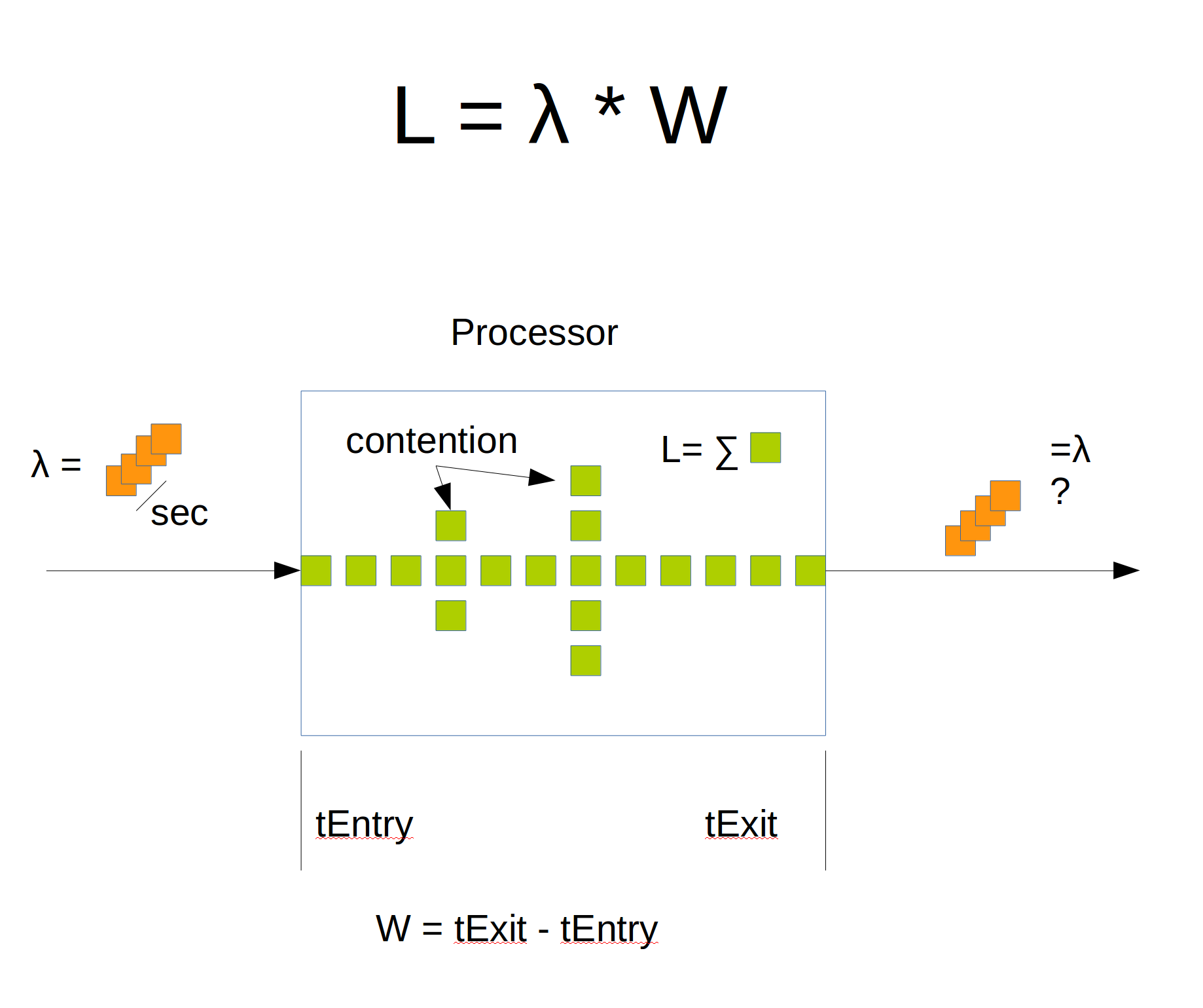 Just my kind of article that Marc Brooker wrote about stories and Little's law. I use stories a lot more than mathematical formulas for two reasons: stories are kind of intuitive and they tend to stick in peoples memory. Little's law says that the number of requests in a queuing systems at any time can be calculated by multiplying arrival rate with the average time spent in the system.
Just my kind of article that Marc Brooker wrote about stories and Little's law. I use stories a lot more than mathematical formulas for two reasons: stories are kind of intuitive and they tend to stick in peoples memory. Little's law says that the number of requests in a queuing systems at any time can be calculated by multiplying arrival rate with the average time spent in the system.
LL can be used for capacity calculations or it can be used to think more about the dependencies in your system. What does "mean concurrency" mean? How spiky is your arrival rate? How much variation is in your processing time? Just painting a diagram of your queues and processing elements gives a chance to mentally change parameters and behavior. What do we need to measure? Should we abort new requests and when should we do so? Should we delay requests which were processed really fast? (think about your clients behavior in this case). Should we try to make all requests equally long? When we have many concurrent requests in processing, what does this mean for contention?
I know Peter Bailis from his excellent work on eventual consistency in NoSQL databases and his clear explanations of isolation levels in RDBMS. From my lecture in distributed systems I know that isolation levels are still a mystery for many developers. A dangerous mystery. Bailis shows that e.g. a missing "read for update" in MVCC systems (like Oracle) or a cheap "read committed" instead of "serializable" allows for a clever attack vector: A DB is put under load and then concurrent transactions from the same account are performed. These TAs read the same values and write the results based on those values. Not locking the "read" during concurrent TAs can cause lost-update effects.
I have long stopped preaching the traditional IT-Sec gospel of software-updates, patching and IDS. Instead, my focus is on damage reduction as there is no way to prevent successful attacks on Intranets. Google is doing it right with "beyondcorp" and the example from nPetya shows nicely how todays IT environment invites malware attacks e.g. through "supply-chain attacks". WIRED magazine just published the story of nPetya frome the perspective of MAERSK - the global shipping and port company. Here, external vendors are compromised and IoT devices download malware from those vendors. The WIRED article is very nice to read but does only cover the results of the attack. But between the lines it i a proof for what Robert Graham says in his paper above: the true problem is the lack of segmentation. He shows that the malware spread laterally through Intranets (mimikatz for MS-networks) using abundantly available local admin rights. It was not a lack of patching ETERNALBLUE, it was the absolute lack of damage reduction techniques in Intranets given the sorry state of security in the worlds most used operating system. Segmentation can reduce lateral spreading, but is is rarely used due to domain trust relationships in Intranets.
Just a side note: have you ever wondered why NIC based firewalls never took off? They have very easy rules due to the fact that they have to protect only one machine and not a full DMZ? They are harder to attack from the host (unlike host-based firewalls).
 We are making progress on our traffic measurement project. The intention is to have a cheap and easy solution that allows citizens to measure the traffic flow in their region. Noise, type of vehicle and other parameters are measured. A group of four students at HdM built a prototype system and a model for display. Currently we are using ultrasound sensors but we might use LIDAR in the near future as well. Trucks are identified through a sensor pair mounted higher than the ones for cars. The loudness helps to distinguish small delivery vehicles like the Sprinter from Daimler.
We are making progress on our traffic measurement project. The intention is to have a cheap and easy solution that allows citizens to measure the traffic flow in their region. Noise, type of vehicle and other parameters are measured. A group of four students at HdM built a prototype system and a model for display. Currently we are using ultrasound sensors but we might use LIDAR in the near future as well. Trucks are identified through a sensor pair mounted higher than the ones for cars. The loudness helps to distinguish small delivery vehicles like the Sprinter from Daimler.
In fall, two bachelor thesis will tackle some more problems like using LIDAR and machine learning e.g. to create a fingerprint of vehicles for tracking.
The project might even more relevant as the EU is now tightening the screws about traffic noise too. The regulations for noise measurement somehow remind me of the way fine dust and NO2 pollution are measured in cars. Once I am through with the law and regulations regarding traffic noise, I will post what I have learned.
Dr. Scheffold speaks after almost 40 years of software development with authority, when he talks about hypes and buzzwords dominating good software practice. When is "flexibility" an anti-pattern instead of a good thing? At least when it really means sloppy programmed classes which do not enforce their constraints. He also gives a nice example that caused real problems in production. He urges us to stay away from mere hype and hone our abilities in robust software development.
On a sideline: My colleage Prof. Roland Schmitz talked at our GDPR event about the new TLS3.0 and what it changed. And it looks like it did right to dispose of dangerous protocol downgrade options in older protocols like SSL. When flexibility introduces non-determinisms or attack vectors it surely has turned into an anti-pattern. The article is in German language
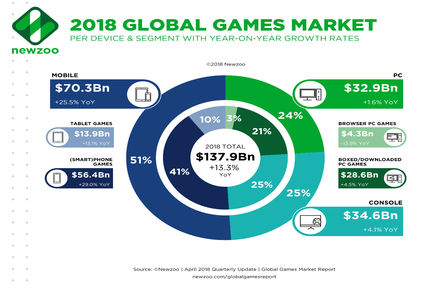 Game development is much more than design, arts and fun. It is about platforms, publishing, marketing and last but not least money. So this time the focus is not on game tech.
Game development is much more than design, arts and fun. It is about platforms, publishing, marketing and last but not least money. So this time the focus is not on game tech.
Agenda: Wann und Wo? am 15.6.2016 um 14.15 im Audimax 011, Nobelstrasse 10, Stuttgart. Wie immer wird der Event aufgezeichnet und kann unter https://events.mi.hdm-stuttgart.de verfolgt werden. Ein chat für Fragen aus dem Internet ist ebenfalls verfügbar. Der Event ist kostenlos und offen für Interessierte aus der Industrie und Akademie sowie für Privatleute.
14.15 Welcome, Prof. Walter Kriha
14.20 "eSports - Neuer Marketingkanal für Spielemacher?" , Mike Fischer, HdM VS
14.50 „Indie-Publishing: itch.io als (gute) Alternative zu Steam?“, Daniel Rottinger ,
HdM Studiengang PR und Indie-Team How to Dev a Morgue
15.25 Pause
15.30 "Indie-Publishing auf Konsolen: Just do it!", Benedict Braitsch, HdM Studiengang OMM
und Strictly Limited Games
16.00 "Mayhem Heroes" - Präsentation zum Milestone vom Games Praktikum HdM,
Danny Fearn und Team
16.30 Pause
16.40 "Game Dev beyond Gaming", Andy Stiegler, Creative Technologist,
Strichpunkt Design
Any questions? mail to: kriha@hdm-stuttgart.de
Todd Hoff quoted a book which claims that physics got blinded by math. beauty and lost its connection to reality. And he asked whether this could be the case for software development as well. Well, this is wrong. We don't do reality (aka empirical verification). Read on.
In our journal club we were dealing first with homomorphic encryption (really hard...) then with elliptic curve crypto (not so hard) and with the question raised about the effects of quantum computing on encryption we landed right in Shlor's algorithm. Some good papers and especially videos made the topic a bit more clear and brought some surprising results. Read on.
A few comments on the consequences of TTS technology getting more natural every day. About identity becoming a digital property and various sorts of attacks on human-digital assistant communication.
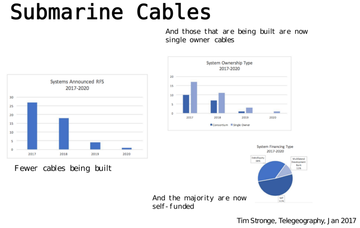 It is amazing what can be learned from IPV4 addresses and submarine cables about the dominant communication structure of the Internet. A short discussion of two papers from G.Houston.
It is amazing what can be learned from IPV4 addresses and submarine cables about the dominant communication structure of the Internet. A short discussion of two papers from G.Houston.
Is this the right time to start a new social network? What are the features needed to replace Facebook? Should it be distributed or federated? A short discussion of social networks.
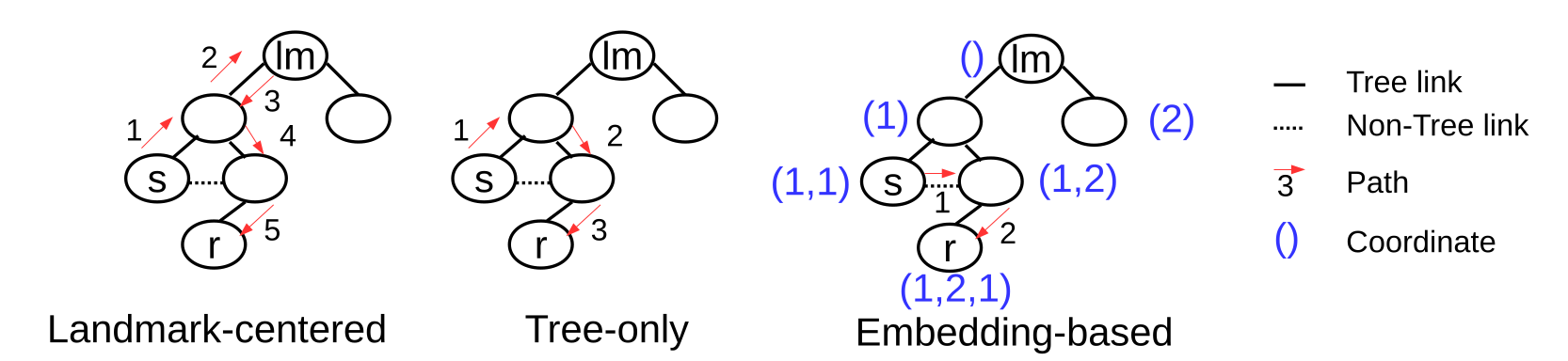 A short discussion of path based transactions and the routing technology needed. It took eight people to make some sense out of it.
A short discussion of path based transactions and the routing technology needed. It took eight people to make some sense out of it.
 When do you use GraphQL? What is the difference to REST? Two short tutorials give you the basic know-how on this technology. And some good design rules for APIs are thrown in as well.
When do you use GraphQL? What is the difference to REST? Two short tutorials give you the basic know-how on this technology. And some good design rules for APIs are thrown in as well.
 Why is digital transformation the core topic for an Interaction Day? Shouldn't we talk about pixels, UI and UX on such a day? Learn about the fast change that is happening in Germanies industry and which affects the way we work deeply. It looks like the industry did read the papers on corporate culture and agility from Netflix, Spotify and others very carefully and is now trying to speed up development using some of the organizational and/or software architectures from the Silicon Valley unicorns.
Why is digital transformation the core topic for an Interaction Day? Shouldn't we talk about pixels, UI and UX on such a day? Learn about the fast change that is happening in Germanies industry and which affects the way we work deeply. It looks like the industry did read the papers on corporate culture and agility from Netflix, Spotify and others very carefully and is now trying to speed up development using some of the organizational and/or software architectures from the Silicon Valley unicorns.
 Learn about three simple rules for great teams.
Learn about three simple rules for great teams.
 On April 13th Prof Borwardt will hold a talk on Big Data at the University of Esslingen. It starts at 16.00 at Flandernstr. 101, room H4. I am looking forward to the latest research on big data from a well-known expert.
On April 13th Prof Borwardt will hold a talk on Big Data at the University of Esslingen. It starts at 16.00 at Flandernstr. 101, room H4. I am looking forward to the latest research on big data from a well-known expert.
A short comment on an almost prophetic paragraph from Yucal Harari's book "homo deus" and the current dilemma of western politics.
Frequently over the last couple of years I had a tummy feeling, that we would should look more carefully at byzantine protocols for consensus instead of always depending on a simple fail-stop error model. A discussion of Byzantine protocols in the context of blockchain sytems raised some interesting questions on conspiration and control by external entities.
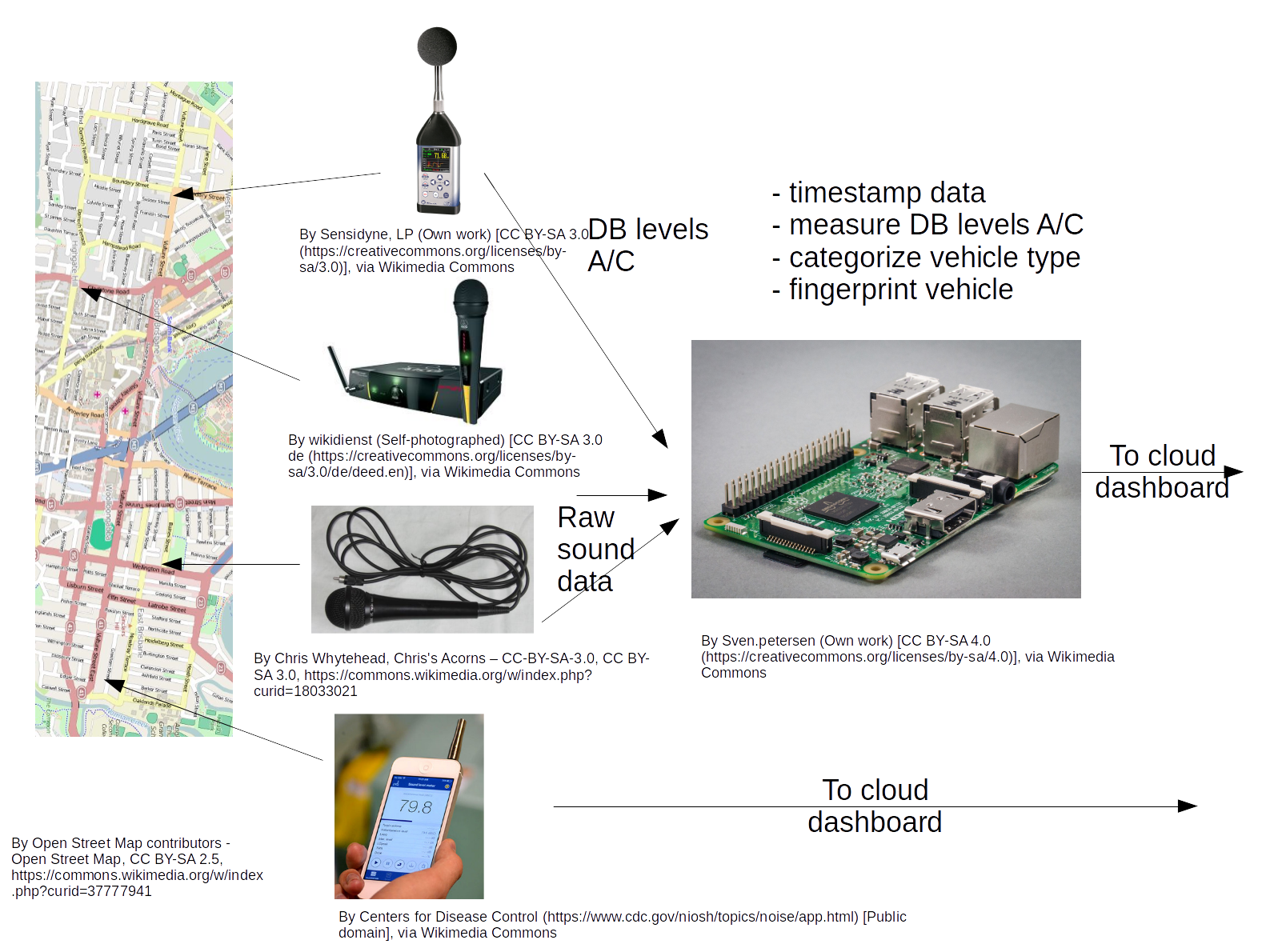 This is an idea for a summer term software project or a thesis. Measuring traffic usually requires expensive devices and is therefore very hard to achieve for small groups of citizens. Cities and villages have little interest in gathering those data, as they could lead to increased awareness, e.g by discovering massive toll avoidance or nightly truck traffic. Sound level meters are available, but they are usually standalone devices, expensive and do not work with Linux. Counting and categorizing traffic is beyond them. Read on to learn about the requirements.
This is an idea for a summer term software project or a thesis. Measuring traffic usually requires expensive devices and is therefore very hard to achieve for small groups of citizens. Cities and villages have little interest in gathering those data, as they could lead to increased awareness, e.g by discovering massive toll avoidance or nightly truck traffic. Sound level meters are available, but they are usually standalone devices, expensive and do not work with Linux. Counting and categorizing traffic is beyond them. Read on to learn about the requirements.
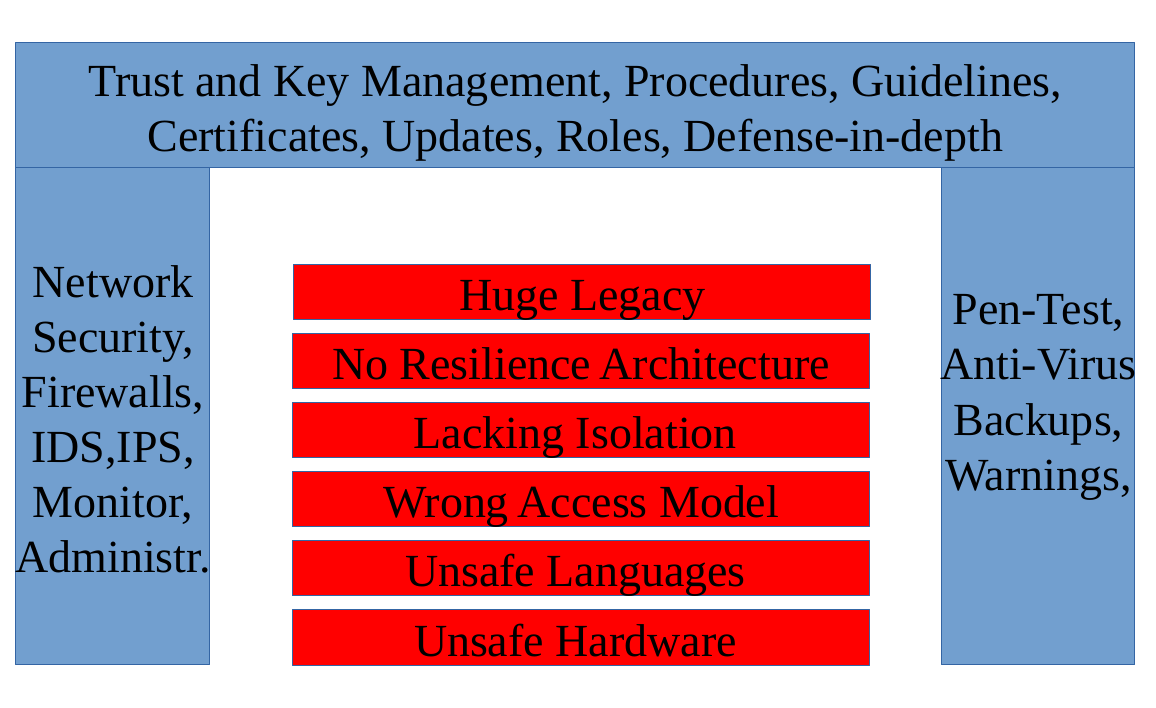 A short article triggered by Thorvalds response to the Google team, Coylers discussion of Daniel Bernsteins famous qmail paper and the first CPU security bugs.
A short article triggered by Thorvalds response to the Google team, Coylers discussion of Daniel Bernsteins famous qmail paper and the first CPU security bugs.
 Another reflection on one of my courses, this time over a longer period of time. The forces that made me change it into a largely theoretical lecture are described and a short overview of the developments in distributed systems is given.
Another reflection on one of my courses, this time over a longer period of time. The forces that made me change it into a largely theoretical lecture are described and a short overview of the developments in distributed systems is given.
A short note on experiences made with a so called journal club where a small group of students and a lecturer read the same papers and discuss them in a seminar. A very light weight form of class with surprising benefits for both lecturers and students. Learn about the benefits and how to run a journal club.
A short note on experiences made with flipped learning in a course on concurrency and parallelism. Turns out that many students profit from micro-exams because they realize their reading deficits quite clearly.
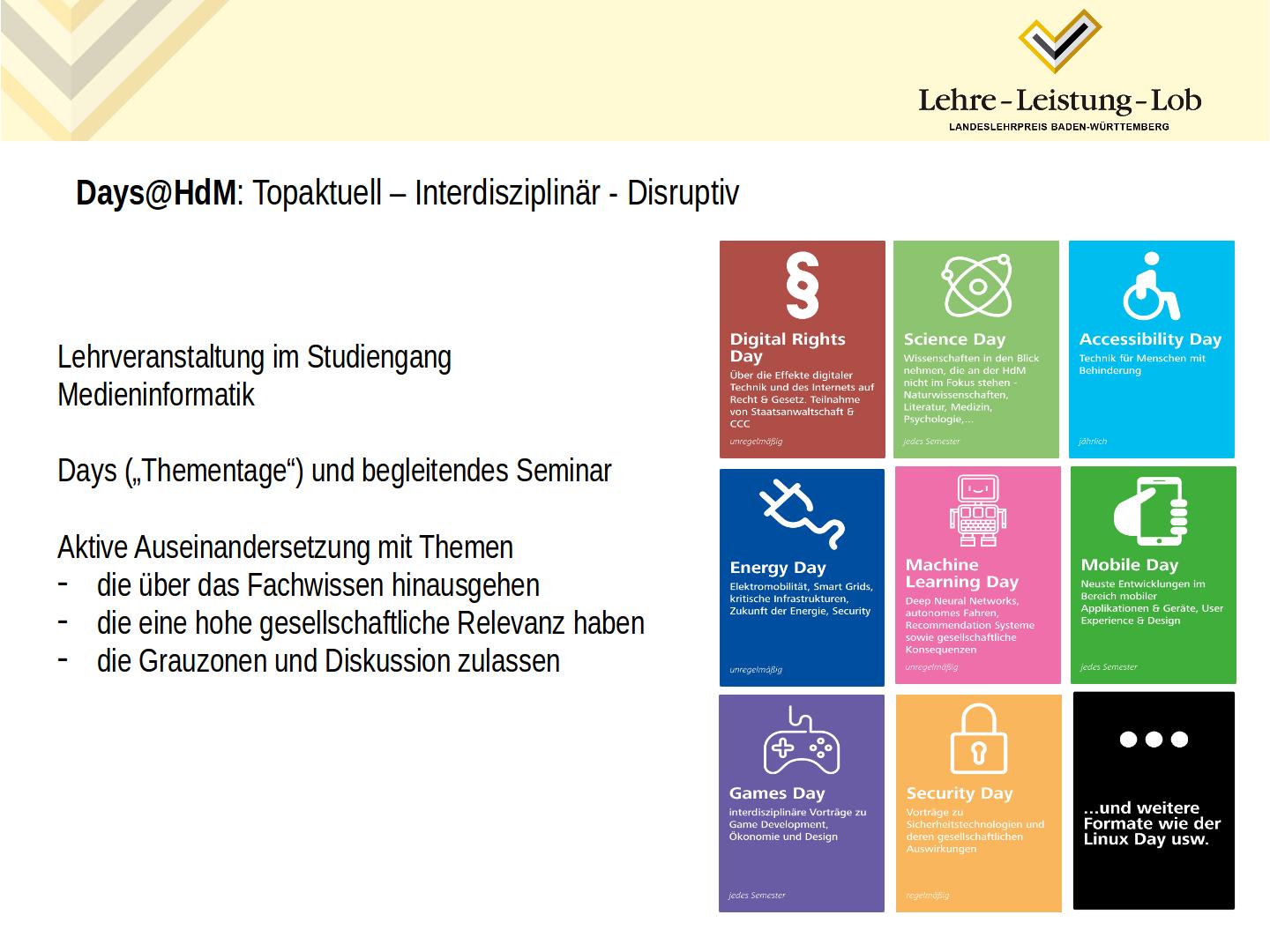 a special type of lecture that won the University teaching price in 2017 (unfortunately the description is in German and I didn't have the time to translate it yet.) And a big thanks to Verena Kersken for helping me with the presentation!
a special type of lecture that won the University teaching price in 2017 (unfortunately the description is in German and I didn't have the time to translate it yet.) And a big thanks to Verena Kersken for helping me with the presentation!
Four talks on technical or design aspects of game development
Note
Friday 23. June 2017, 14.15 - 18.15 at HdM, room 056. A live stream and chat is available. For directions go to hdm homepage..
Dr. Frisch of IBM Böblingen will give a talk on quantum computing at IBM on 21 June 2017 at HdM, 17.45-19.00. Stay tuned for more information. Some really interesting questions come to mind: will QC wipe out existing security algorithms? Are there algorithms which are resistent? How are QC specialist dealing with quantum effects like entanglement? What other areas will be affected by QC? A short intro .
A nasty talk on fundamental safety problems in software land and three proofs.
Some statements on overprotecting students and a nice quote from Nassim Nicolas Taleb.
How do you get the necessary data from social networks in an automated way? The workshop will present our work on a social bot and gather ideas for further tool development to support research in social media. Anybody can attend.
An interesting comparison of distributed vs. local processing of social graphs. Efficience vs. scalability and the new trend of memory centric computing.
Finally a large scale cloud environment in Germany. Dennis Grewe and Julian Weiss of Bosch GmbH showed the architecture, key projects and future plans behind the Bosch cloud.
A very interesting talk about 3D-printing of organic components, the innovative organization behind it and its future uses. Also a bit on CRISPR - the DNA manipulation tool that might get someone a nobel price soon.
 Well, is e-mobility dead or what? What are the current problem areas and what kind of solutions are companies developing right now e.g. with respect to intelligent charging? Are e-cars economically feasible for companies? Can you go across Germany with an e-car? Learn more about e-mobility at our first E-Mobility Day at HdM with talks from Fraunhofer IAO, Vector Informatik and BridgingIT.
Well, is e-mobility dead or what? What are the current problem areas and what kind of solutions are companies developing right now e.g. with respect to intelligent charging? Are e-cars economically feasible for companies? Can you go across Germany with an e-car? Learn more about e-mobility at our first E-Mobility Day at HdM with talks from Fraunhofer IAO, Vector Informatik and BridgingIT.
Note
Friday 10. June 2016, 13.45 - 17.15 at HdM, room 056. A live stream and chat is available. For directions go to hdm homepage. And last but not least are we going to test our new smartphone solution for live streaming of events.
We are closing the seminar on concurreny and parallelism with a little workshop. A case from the industry will be discussed in the context of several different technologies.
Note
Friday 15. January 2016, 14.00 - 18.00 at HdM, room 056. A I am not sure about a live stream due to the workshop character of this event. It it is available, it can be found here hdm homepage.
Indi development, new gesture recognition interfaces, multiplayer technology, asset creation for virtual reality and of course: lots of demos and previews at our next games day.
Note
Friday 12. June, 13.30 - 19.00 at HdM, room 056. A live stream with chat is provided. As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.
Just a few comments on our talks. There is more to come in fall 2015, when our second Language Day will take place. We will have talks on Javascript, C#, Rust and functional languages.
Given the sad state of IT-Security, it is about time to fix the basics...
Still our most important tool - the programming language, is undergoing drastic changes. New paradigms are introduced, new languages pop up almost every week. What makes a good language in Internet times? Fit to support agile development, continuous delivery and increasing demands for security and usability. Learn about new developments in our first language day. The next one in the winter will probably cover Javascript, C# and Rust/Dust/D.
Note
Friday 10th April, 13.30-17.30 at HdM, room 56. A live stream with chat is provided. As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.
In this post-Snowden area we are taking a close look at secure software, critical infrastructures and ways to conquer the threats to critical infrastructures and individual exposures. Specialists from 1&1, Bosch and mpc are joining us for this long overdue event.
Note
Friday 16th January, 13.30-17.30 at HdM, room 56. A live stream with chat is provided. As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.
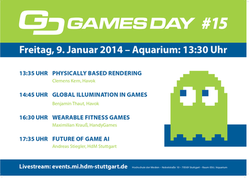
A bit more technical than the last ones, this games day will deal with advanced concepts in realtime lighting, physically based rendering, games on smart watches and artificial intelligence in games.
Note
Friday 9th January, 13.30-19.15 at HdM, room 56. A live stream with chat is provided. As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.

It was about time for a repeat of our Developer Days at HdM. This time we will have three talks about software design, architecture and frameworks for successfull enterprise software. All based on many years of practical experience with difficult decisions regarding designs. Join us for this interesting session. Developers, architects, consultants and project managers as well es members with akademic background welcome!
Note
Friday 7th July, 13.30-17.15 at HdM, room 11 (please note that the room has changed!). A live stream with chat is provided. As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.

Is the future of games in virtual reality? What is the current state of VR? How does it feel to play a game made for the Oculus Rift? (In case you don't own one: how about building your own? Take a look at the latest gadget from Google I/O . How does it feel to develop a game for virtual reality? Get some background information and practical know how at this games day. And discuss your vision of the future with us. Please notice the change in the agenda: we'll let you watch another game at the end (:-)
Note
Friday 4th July, 13.30-16.45 at HdM, room 56. A live stream with chat is provided. As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.
Get a better understanding of your visitors! Learn how to collect and analyse behavioral data. Meet tool vendors and users of analytic tools and learn how to test your business profile.
What can you learn from looking at search requests leading to your platform? You are running youtube videos - did they help to increase the number of visitors? There are many things you can learn from analysing the behavioral data of your visitors. But before you can do so, you must collect the data and learn to use the tools needed for analysis and reporting. They are a must for a successful site or blog. In case you are just a user of internet sites, you can get a better understanding of data collection on the web and why it is - to a certain degree - absolutely necessary for sites.
Note
Friday 23rd April, 13.30-16.45 at HdM, room 56. A live stream with chat is provided. As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.
Talks and discussions on current legal affairs around the Internet. Intellectual property rights, escpecially software patents, the NSA and Anonymous and last not least the Redtube streaming scandal. In all these cases, technological opportunities meet economic stakeholders on the battle field of laws and legal actions. And not every technology is legal and not every legal claim is justified.
Note
Friday 25th April, 13.30-16.45 at HdM, room 56. A live stream with chat is provided. As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.

It's all about speed: how to build fast and responsive web applications, quick application design within the browser and last but not least the realtime and peer-to-peer features of the new WebRTC standard. The 7th webday at HdM lets you meet with experts in those areas and extend your knowledge of HTML5.
Note
Friday 10th January, 13.30-16.45 at HdM, room 56. A live stream with chat is provided. As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.
Im Rahmen des Tags der Lehre an der HdM halte ich einen kleinen Vortrag zu meinen "Days".
Mittwoch, 4.12.2013 um 16.45 in 013 in der Nobelstrasse 10, Stuttgart-Vaihingen. Der Talk "Blick über den Tellerrand" beschreibt ein wenig die Hintergründe, Zielsetzungen und Tricks.

The image shows a solution for a rather hard problem: capturing live discussions with little equipment and almost no manpower. And to top it off: in any room. So we are talking a mobile solution too.
Note
The prototype has been usability tested successfully and all it takes now is somebody who can turn it over into a ruggedized product. Let me know if you can do it!
This week I realized, that splitting up requests into tens or hundreds of subrequests is still a rather hard problem, due to the long-tail distribution of response times. A portal is a typical fan-out architecture. In 1999 I found some solutions for fan-out like controlled backends, replication and incomplete (tainted) requests. Google of course goes much further today.
Strictly timed requests, distributed loads and a close look at everything from the CPU over network buffers, data structures in memory etc. are in the toolbox.
You think milliseconds is fast? Think again. Think about putting algorithms into FPGAs. Think about creating algorithms that fit into L1 caches. Algorithms which do not need much memory and which do not touch data more than once. Learn about the use of one-pass algorithms from HFT. And start thinking about all the places in our computing infrastructure, where latency hides.
Is the Internet a good model for power grids? What can energy engineering learn from IT and what should it better do in its own ways? Which patterns work in both areas? What makes a robust solution? This is a short talk on some ideas gained from the Smart Grids Week in Salburg this year. Cultural and technical aspects are covered in my talk on Blackout - on the role of IT in Smart Energy Grids .
Note
Wednesday 27th November, 17.45 at HdM, room 011. As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.
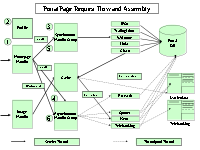
Christian Teutrine, Senior Managing Consultant with Global Business Services, IBM will give a talk on practical experiences with MDA, made in a large project which took 7.5 years from the concept phase to the go-live. 80% of the code had been generated. Mr. Teutrine had the role of a business lead architect in this project, and in his talk, he will look at it from a business architecture point of view: How does MDA influence the contractual situation? The project management? Can agile methods be used with MDA? How well does it work over the years? What if off-shore employees join the project?
This talk is a rare chance to get first-hand experience on the interplay between business and technical aspects in a really large project. It is not so much a technical talk.
Note
Wednesday 4th December, 19.30 at HdM, room 041. Live streaming at can be found at events.mi.hdm-stuttgart.de . As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.
How does Amazon know what we want? Learn about advanced recommender systems which use clever algorithms to match users and items. See how math and computer science shape modern marketing.
Note
Friday 29th November, 14.00 - 17.00 at HdM, room 56. A live stream with chat is provided. As always, the event is free of charge and open to the interested public. Directions can be found at the hdm homepage.
It was more than time for a re-structuring and renovation of my site. I considered changing to wordpress but finally decided to stick with my xml-based generative approach. But instead of generating my own navigation I am now using CSS3 (without any javascript) for it. Now comes content cleanup...
 @
@